We are proud to announce an Amulet team members’ successful dissertation. Dr. Taylor Hardin’s dissertation focuses on an end-to-end solution for providing information provenance for mHealth data, which begins by securing mHealth data at its source: the mHealth device.
The dissertation describes a memory-isolation method that combines compiler-inserted code and Memory Protection Unit (MPU) hardware to protect application code and data on ultra-low-power micro-controllers. The security of mHealth data outside of the source (e.g., data that has been uploaded to smartphone or remote-server) is then addressed with Amanuensis, a health-data system, which uses Blockchain and Trusted Execution Environment (TEE) technologies to provide confidential, yet verifiable, data storage and computation for mHealth data. The use of blockchain and TEEs introduce identity privacy and data freshness issues, which are explored. A privacy-preserving solution for blockchain transactions, and a freshness solution for data access-control lists retrieved from the blockchain are presented.
To learn more, check out Dr. Taylor Hardin’s dissertation below.
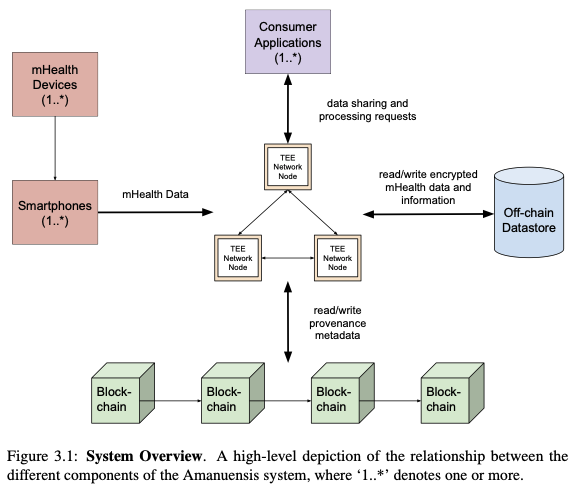
Hardin, Taylor A., “Information Provenance for Mobile Health Data” (2022). Dartmouth College Ph.D Dissertations. 79.
https://digitalcommons.dartmouth.edu/dissertations/79