The Amulet project launched in late 2013 with the vision of “bridging the gap between the type of pervasive computing possible with a mobile phone and that enabled by wearable computing.” Now, almost 10 years, 51 publications, and 29 core members (along with many collaborators) later, Amulet is coming to a close.
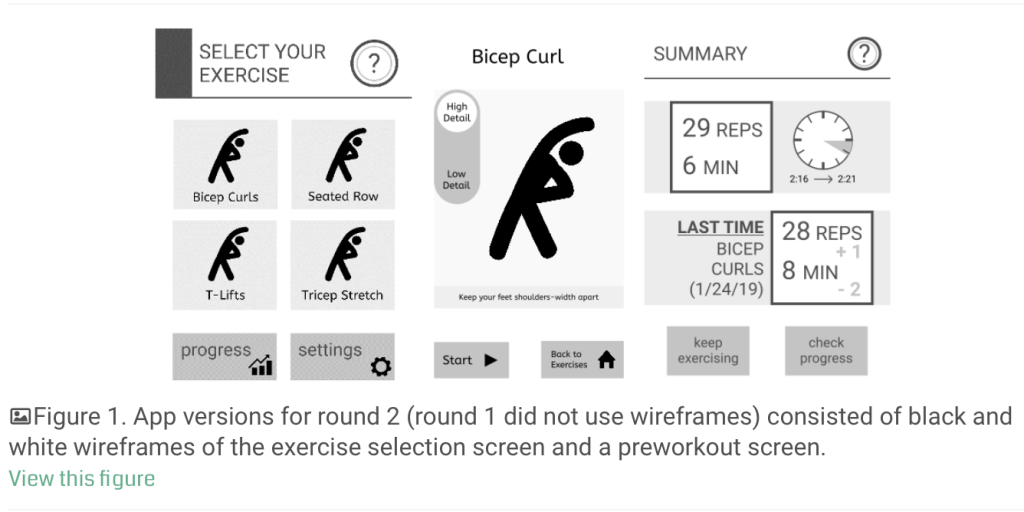
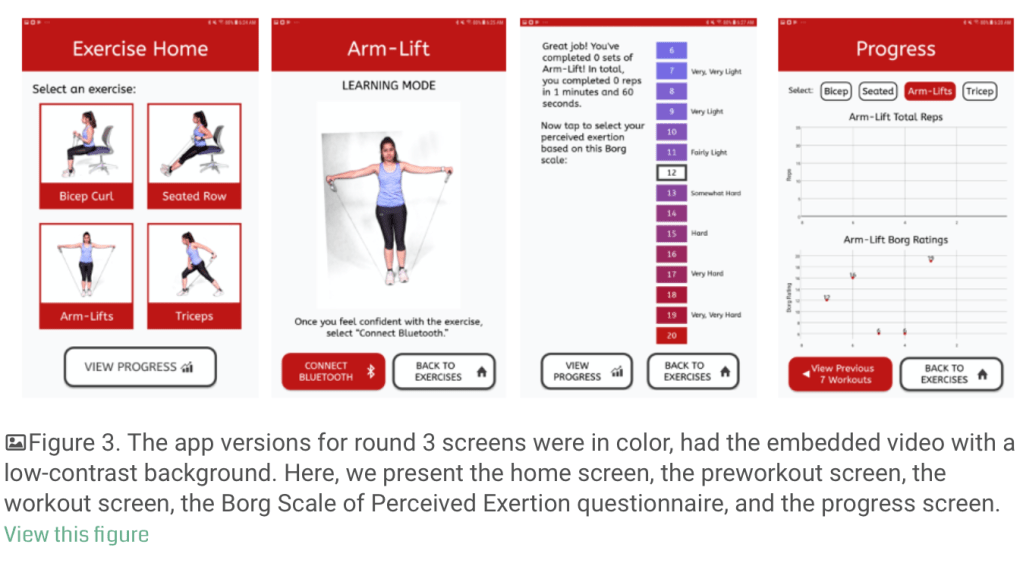
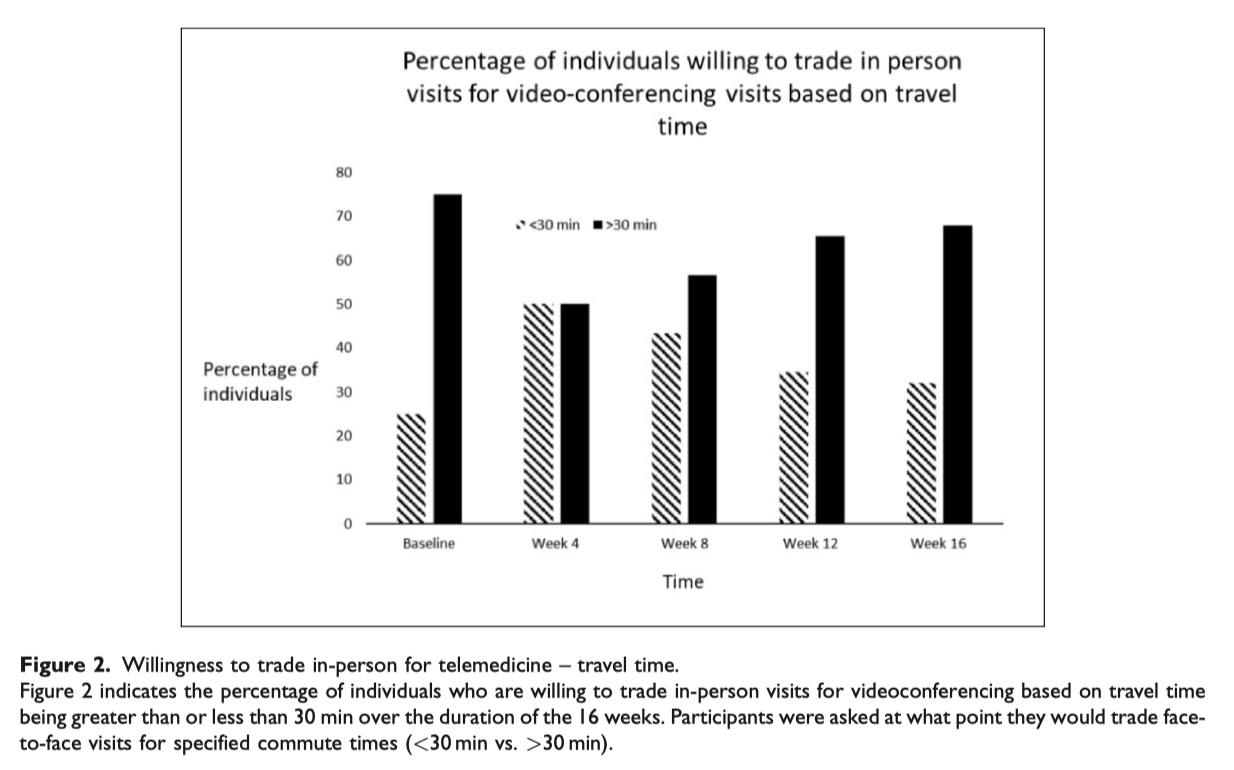
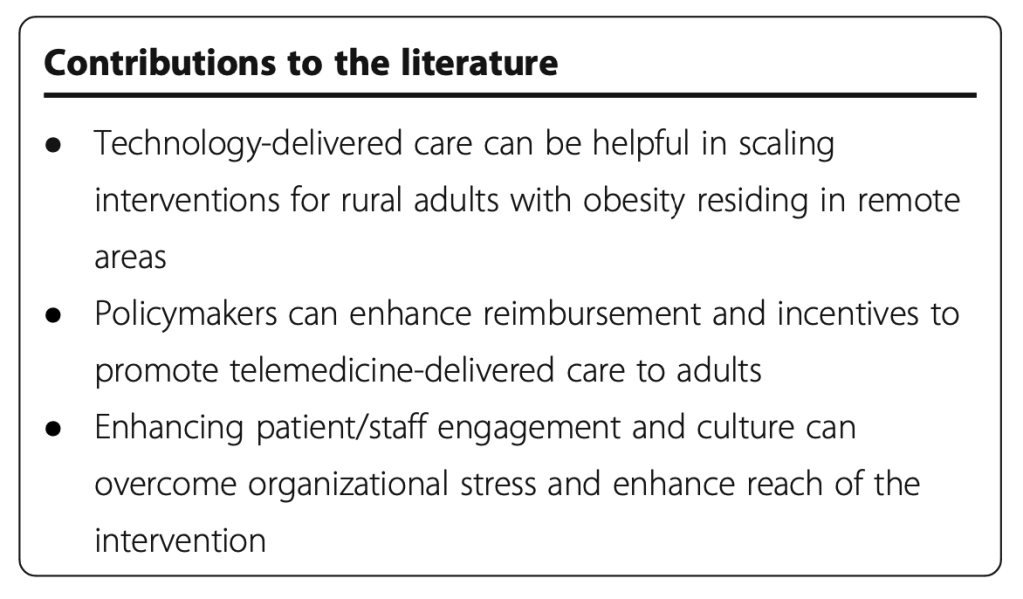
Amulet was featured in Forbes magazine, has been presented to audiences at many conferences and at an mHealth summit near Washington DC, was evaluated on usability in a study amongst rural older adults with obesity, and is impacting continued health research!
Many of our students have gone on to roles in industry and academia after graduation, and Ryan Halter, the Dartmouth co-PI on the project, co-founded a startup company, SynchroHealth, with technology originating in the Amulet project.
The Amulet prototype remains available (open source, open hardware) on GitHub, and our papers are available through our Zotero library.
We thank the countless number of people who have supported the project — from advisors, to NSF program officers, to graduate and undergraduate students, to study participants, to project leads, and to you all who have kept up with the project for its 10-year run.